Some stop gap followed is to have a job running which removes the policy from an IAM user when certain time conditions are met. So basically what we would do is, to have a job that calls an API that removes the policy which restricts an IAM user or group from launching instances. This will make the IAM policy management complex and tough to assess/govern drifts between versions.
After the introduction of the CloudWatch events our Cloud operations started controlling it with lambda functions. Whenever a Instance type is launched it will trigger a lambda function, the function will filter whether it is a specific “C” type and check for the current time, if the time falls after office hours, it will terminate the EC2 instance launched immediately.
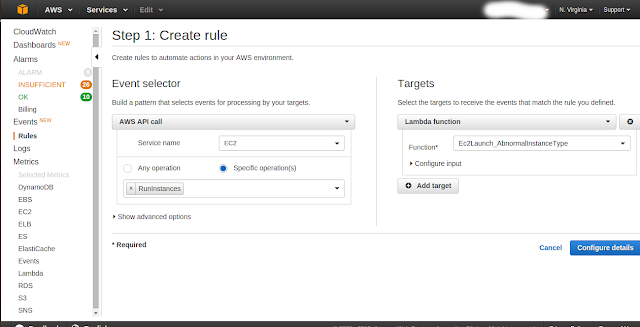
As a first step, we will be creating a rule in Amazon CloudWatch Events dashboard. We have chosen AWS API Call as an Event to be processed by an AWSCloudTrail Lambda function as a target.
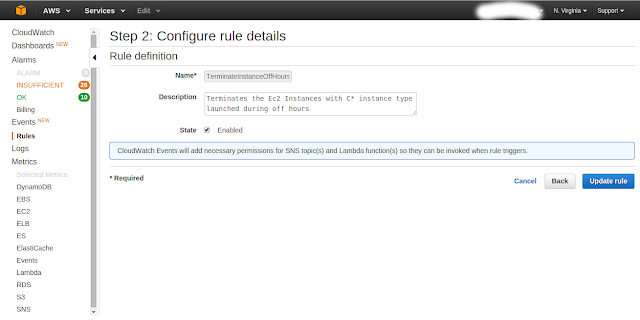
The next step would be configuring rule details with Rule definition
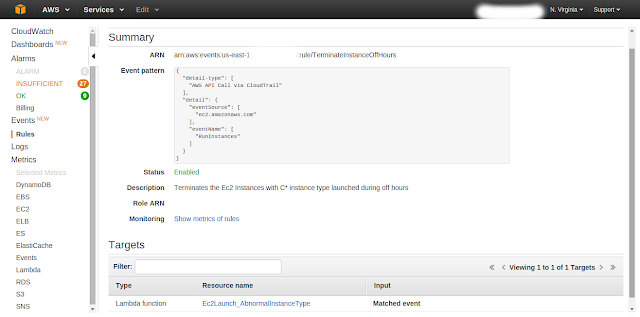
Finally we will review the Rules Summary
Amazon Lambda Function Code Snippet (Python)
import boto3
def lambda_handler(event, context):
#print ("Received event: " + json.dumps(event, indent=2))
#print ("************************************************")
ec2_client = boto3.client("ec2")
print "Event Region :", event['region']
event_time = event['detail']['eventTime']
print "Event Time :", event_time
time = event_time.split('T')
t = time[1]
t = t.split(':')
hour = t[0]
instance_type = event['detail']['requestParameters']['instanceType']
print "Instance Type:", instance_type
instance_id = event['detail']['responseElements']['instancesSet']['items'][0]['instanceId']
print "Instance Id:",instance_id
if( instance_type.startswith( 't' ) and hour > 18 or hour < 8 ):
print ec2_client.terminate_instances( InstanceIds = [ instance_id ] )
GitHub Gist URL: https://github.com/cloud-automaton/automaton/blob/master/aws/events/TerminateAWSEC2.py
This post was co authored with Priya and Ramprasad of 8KMiles